Securing Resources and Private Data Part 2
- November 4, 2022
- 0 replies
- 743 views
Step 5: Limiting Composer Access
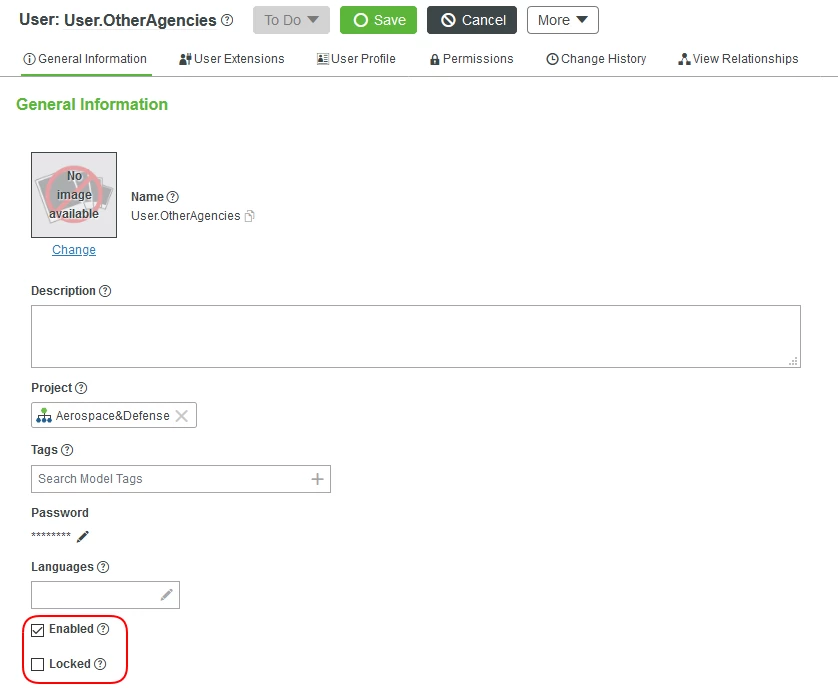
If you would like to limit a User even more, there are a few things you can do. Go back to the Administrator account and open one of the accounts we created, such as User.OtherAgencies, you will notice the Enabled and Locked checkboxes. Enabled allows you to set whether an account can be used in ThingWorx during runtime. Locked dictates whether an account can be logged into at all.
Suppose we would like for the user to only see emptiness when they try to access the Composer. Follow the below steps to limit ThingWorx Composer access even more.
1. Open one of the Users we created earlier, ie User.OtherAgencies and click on the User Profile tab. The user profile configuration allows an administrator to control which categories and entities should be displayed for an individual User.
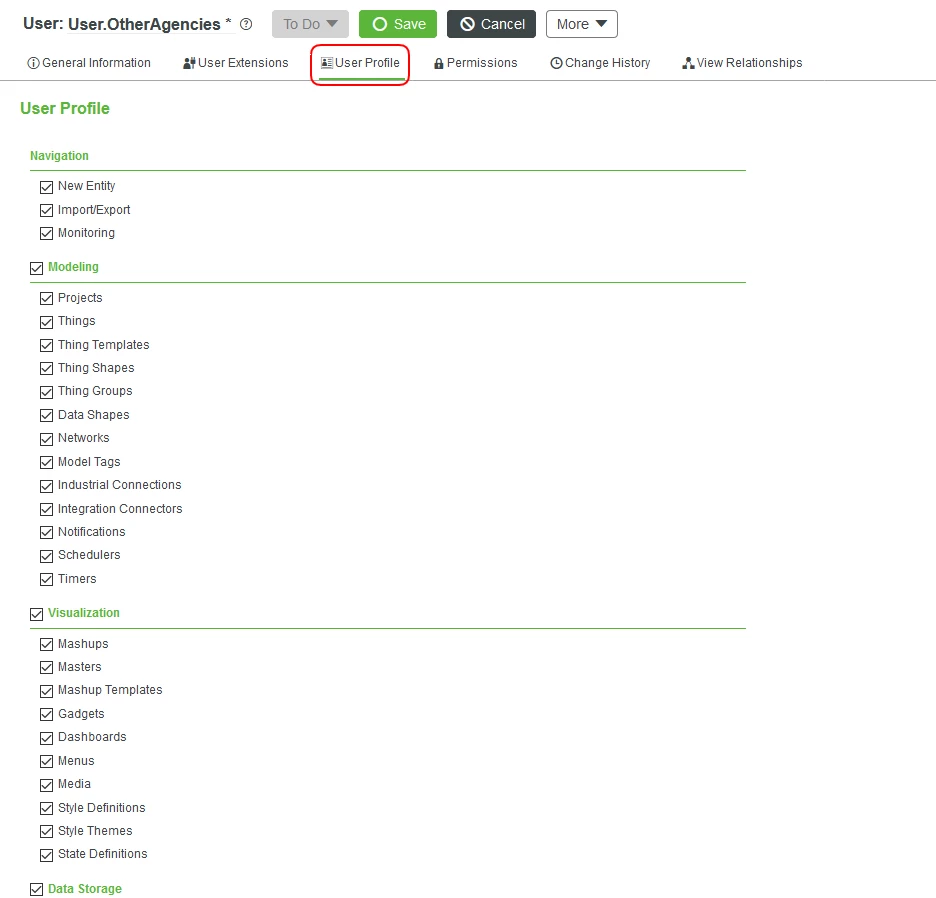
2. You will see various sections and checkboxes. Uncheck all of them to stop access to importing, exporting, creating new Entities, being able to see existing Entities, and much more.
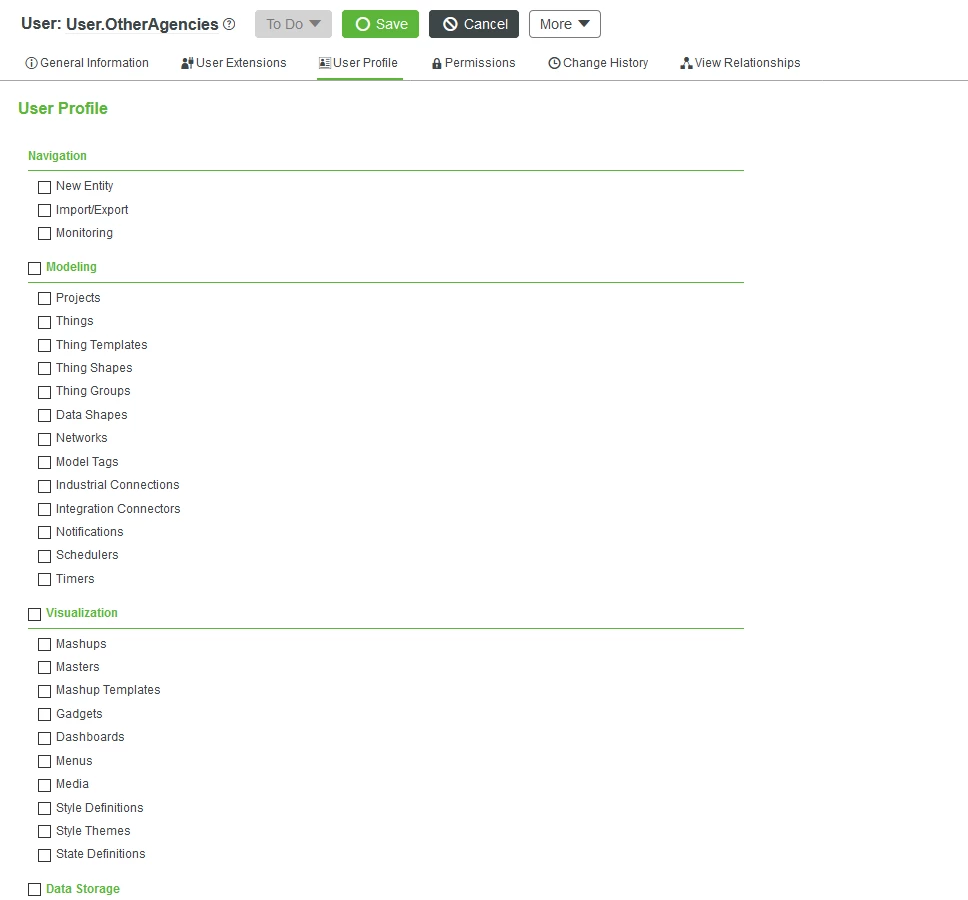
3. Click Save.
Now if you attempt to log into the ThingWorx Composer, you will notice a very difference experience without the ability to see current Entities. Perform this update for all the Users we created, except for User.IT and User.AgencySuperUser.
Step 6: Creating Clearance Levels
ThingWorx does not include default security clearance levels for you. What it does include are Thing Groups. Thing Groups are a reference-able entity type in ThingWorx that allow for Things and Thing Groups as its members. They also provide ThingWorx administrators the ability to manage at scale exposure of Things to only those that require access.
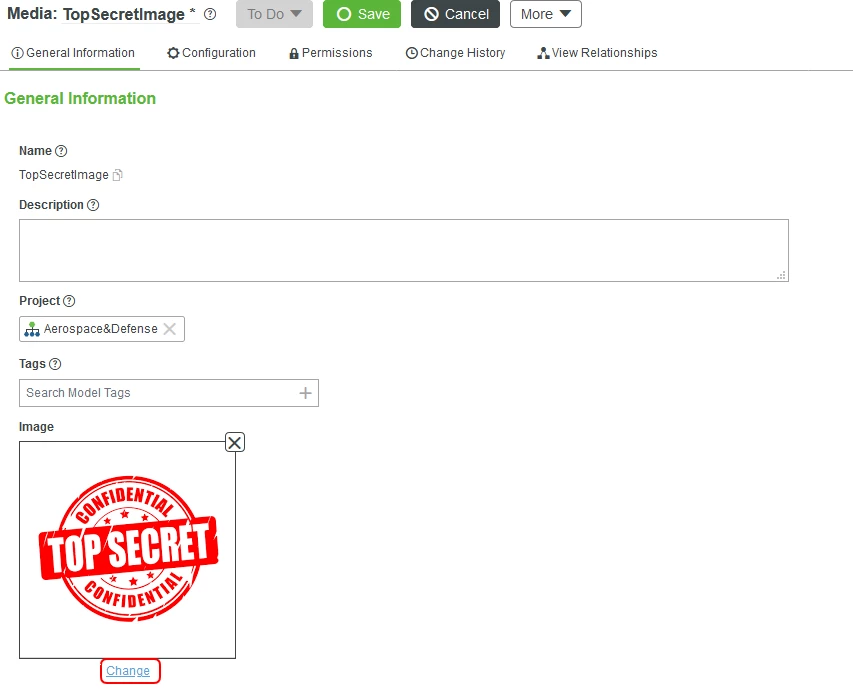
Before we create out first Thing Group, let us create some Entities that will house resources. The first will be an image that is top secret (shown below). In ThingWorx, this would be of type Media. After, we will create a file repository that will contain super-secret documents, a repository for job applications, and another repository for documents that are publicly accessible.
Our Top Secret Image:

Create the Media Entity
Let us store our image in ThingWorx. This image will need extra credentials to access it. This authentication can be performed with a basic username/password setup or SSO utilizing your own configurations.
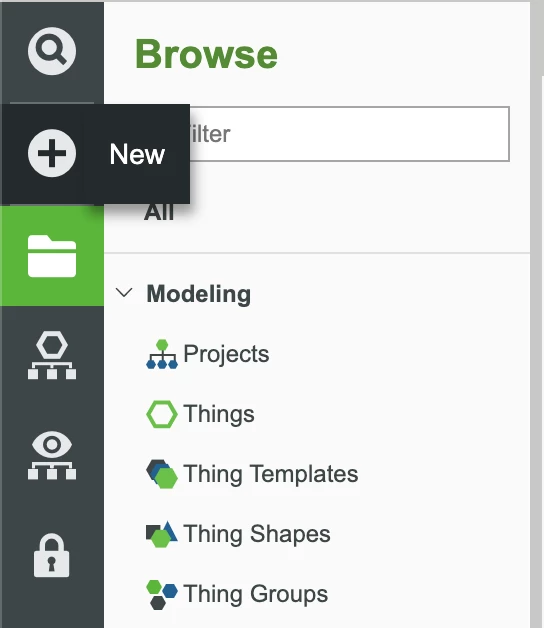
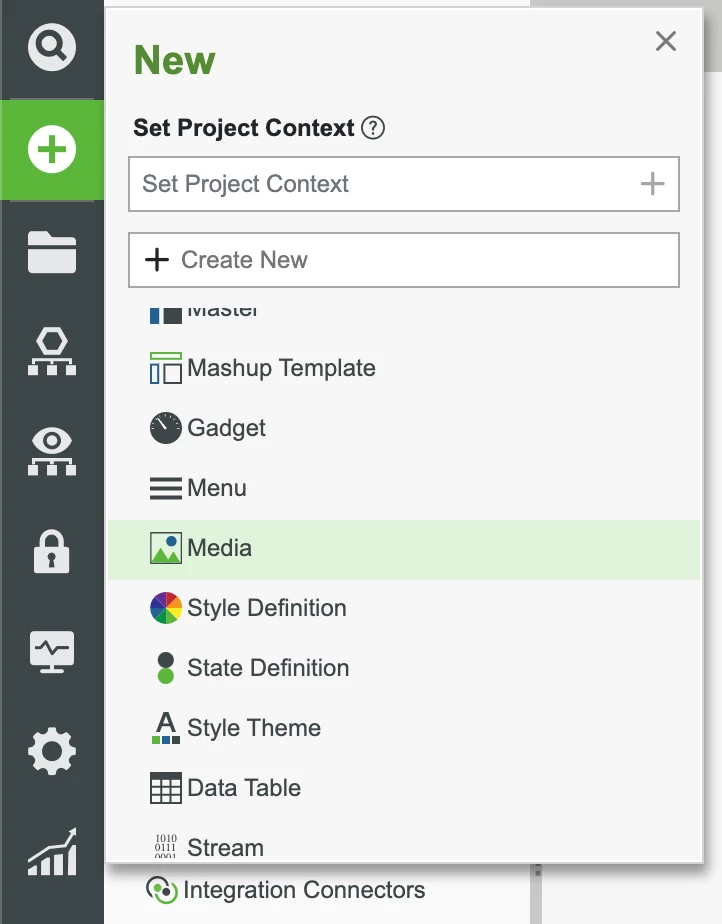
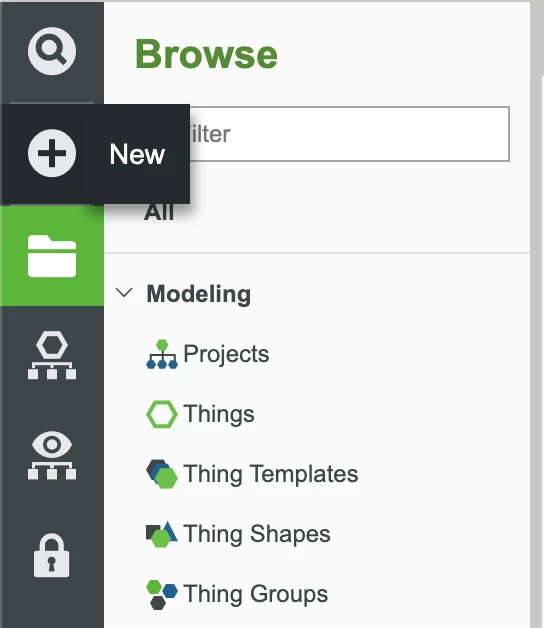
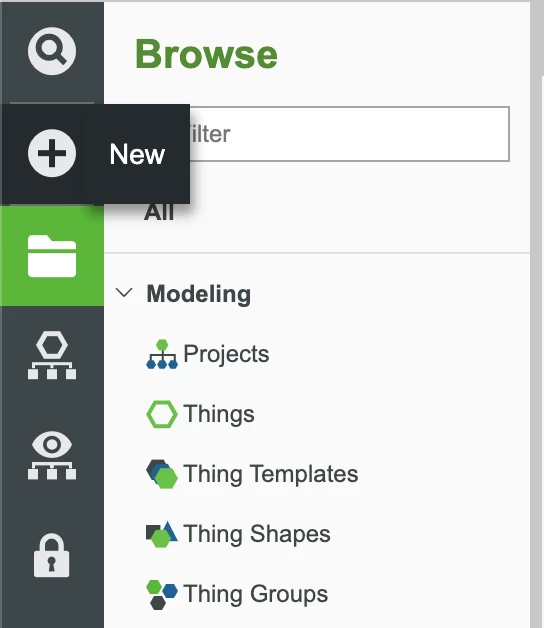
1. In the ThingWorx Composer, click the + New button in the top left.
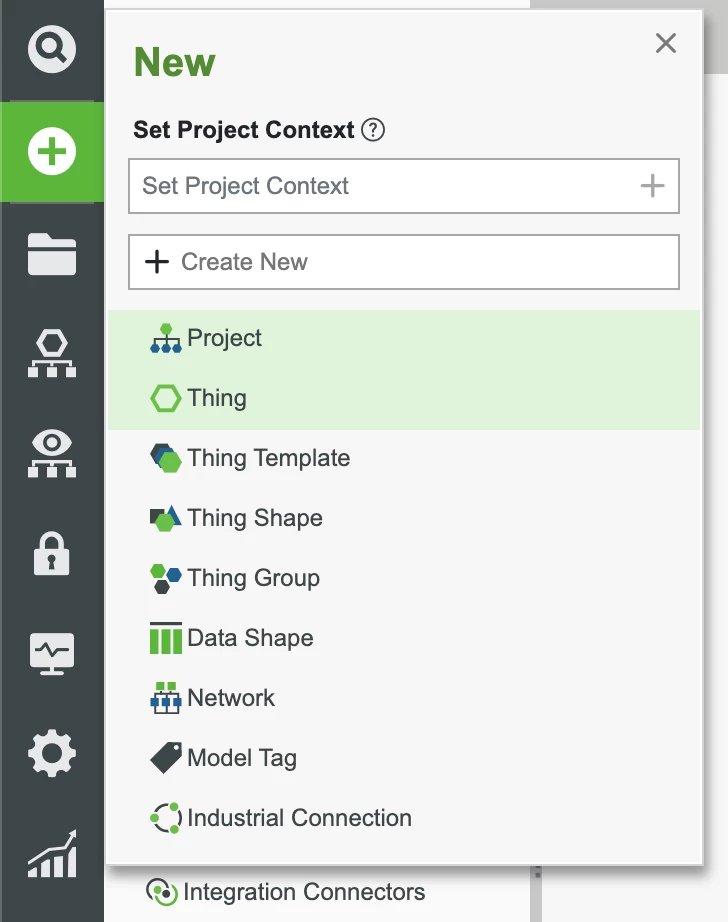
2. In the dropdown list, click Media.
3. In the Name field, use TopSecretImage.
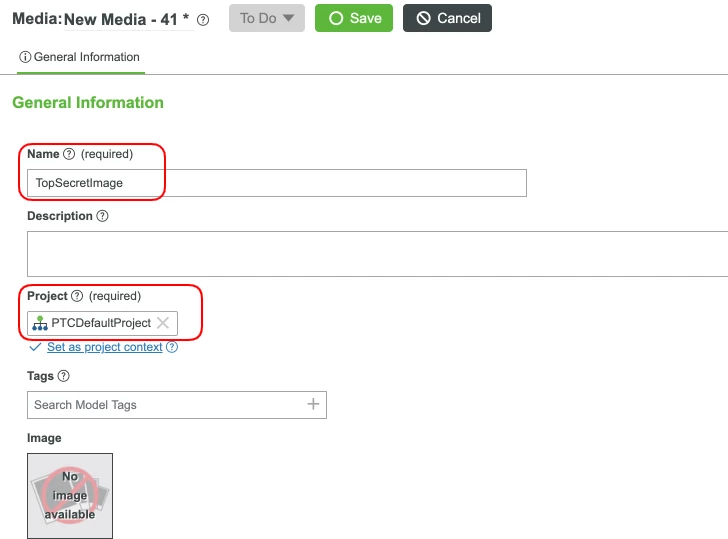
4. Set the Project field to an existing Project (ie, PTCDefaultProject) and click Save.
5. Click Change and add an image or use the image above.
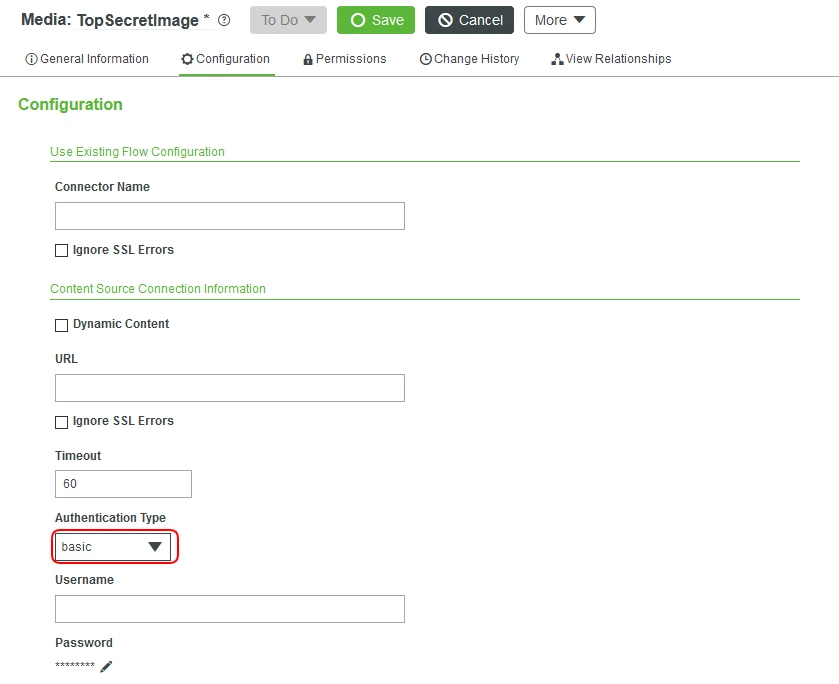
6. Click on the Configuration tab.
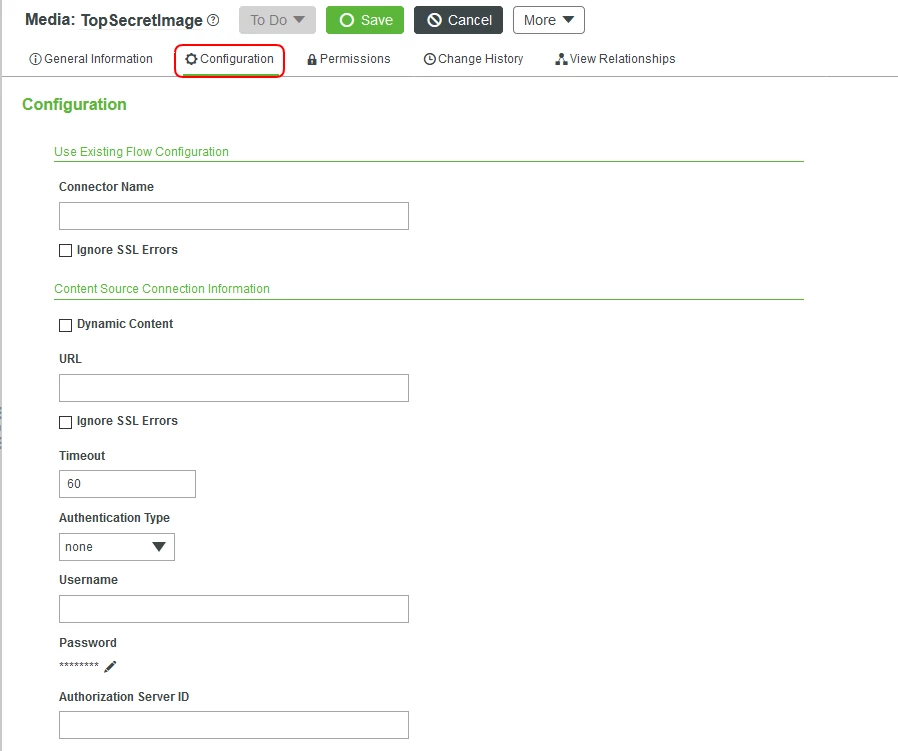
7. For the Authentication Type field, select basic. You can select other types based on your Single Sign On and server level configurations, but we will keep this scenario simple.
8. Set a Username and Password that would be used to access our top secret Media.
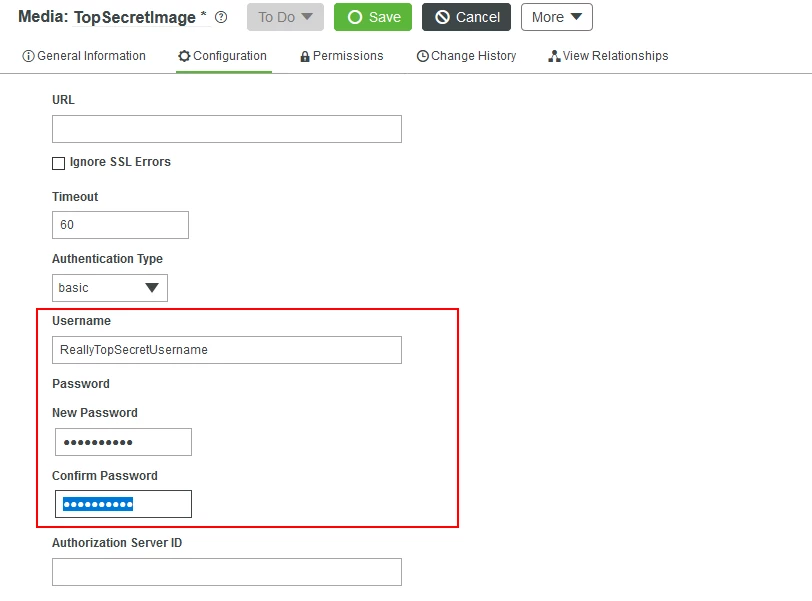
9. Click Save.
Create the File Repositories
Let us create the setup for our repositories.
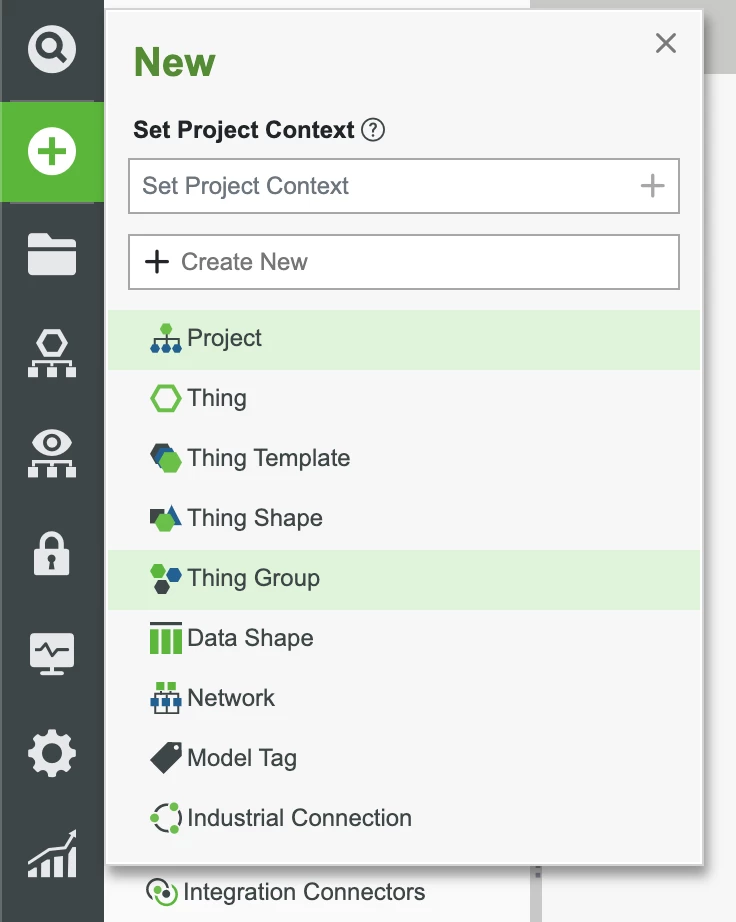
1. In the ThingWorx Composer, click the + New button in the top left.
2. In the dropdown list, click Thing.
3. In the Name field, use TopSecretDocuments and FileRepository as the Base Thing Template.
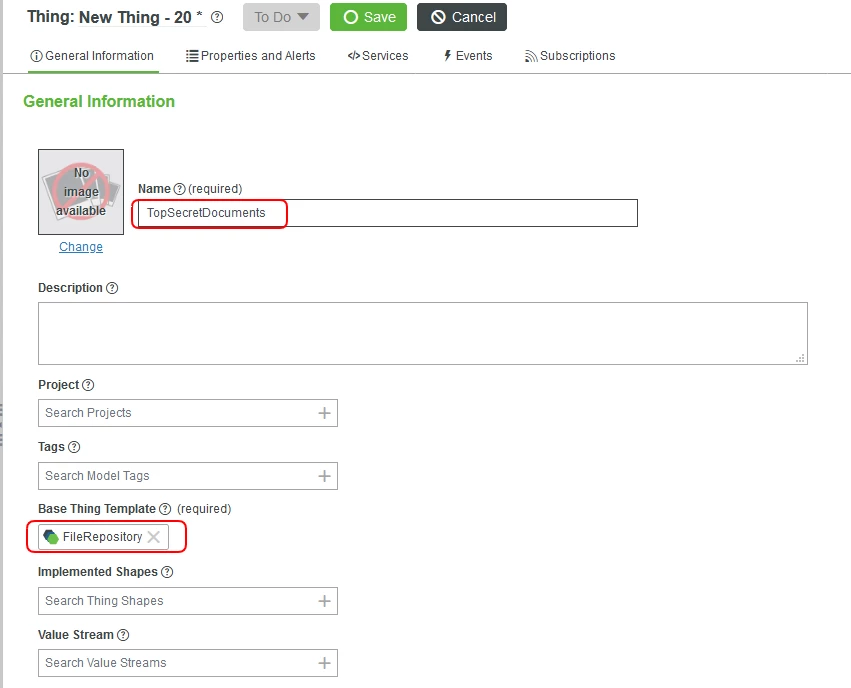
4. Click Save.
5. Repeat steps 1-4 to create two File Repositories titled JobApplications and PublicDocuments.
Security Levels and Resource Lockdown
We now have our several resources and areas for differing levels of access. We will create 3 Thing Groups to mimic security levels. Our top-secret image will exist independently on ThingWorx, but also inside of a file repository for some level of redundancy. That file repository will belong to one Thing Group, while the other two file repositories will have their own separate Thing Groups.
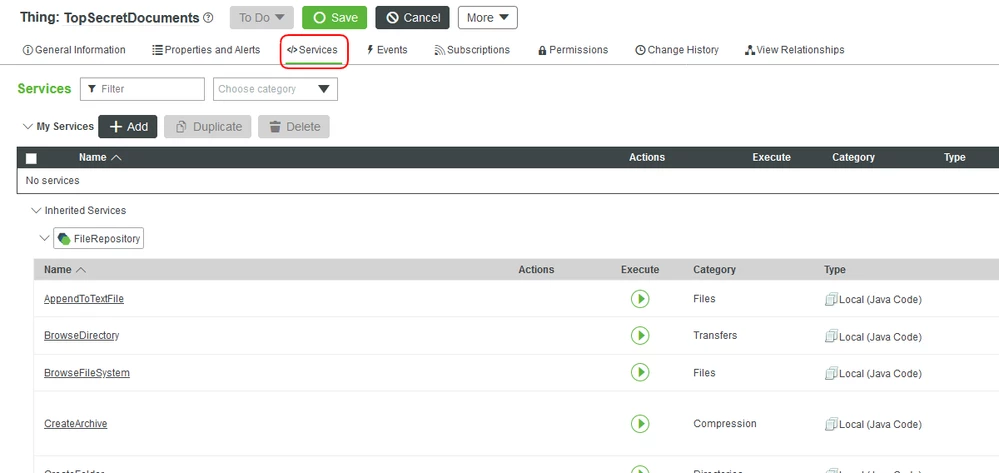
1. Open the TopSecretDocuments File Repository Thing.
2. Click on the Services tab.
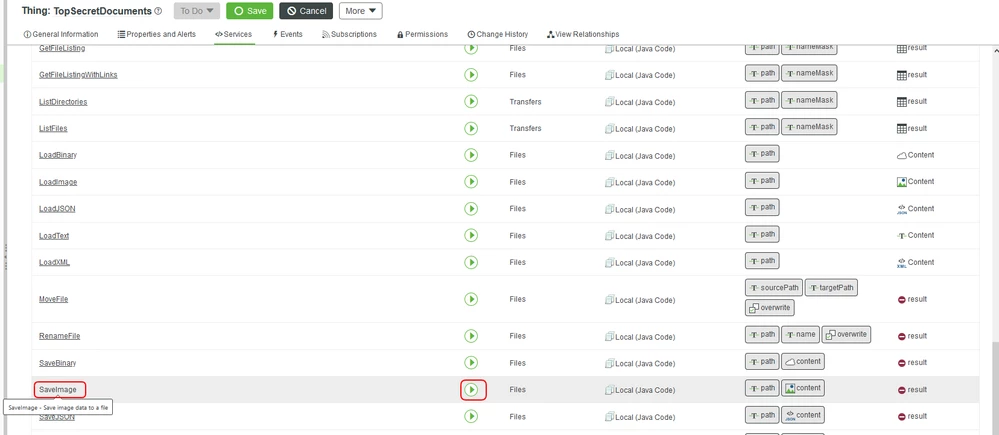
3. Scroll down to the SaveImage and click the play button.
4. Enter a path (such as /SecretImage.png) for the image to reside on the server and click Change to add an image.
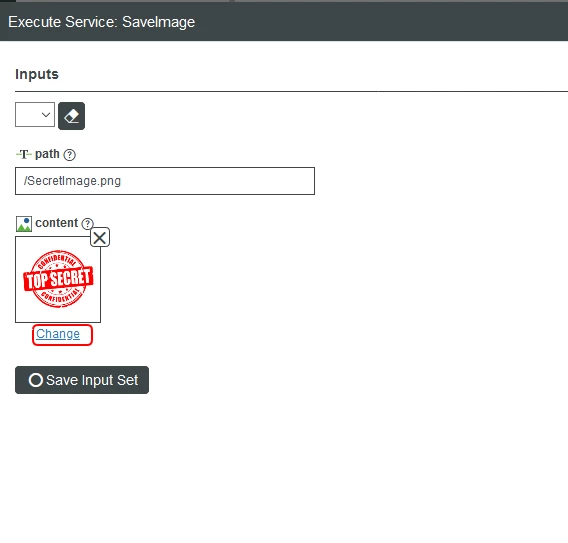
5. Click the Execute button.
You now have your image in a File Repository. Let us add this Entity to a Thing Group, then configure the permissions at the Thing Group level.
1. In the ThingWorx Composer, click the + New button in the top left.
2. In the dropdown list, click Thing Group.
3. In the Name field enter Clearance.Top.
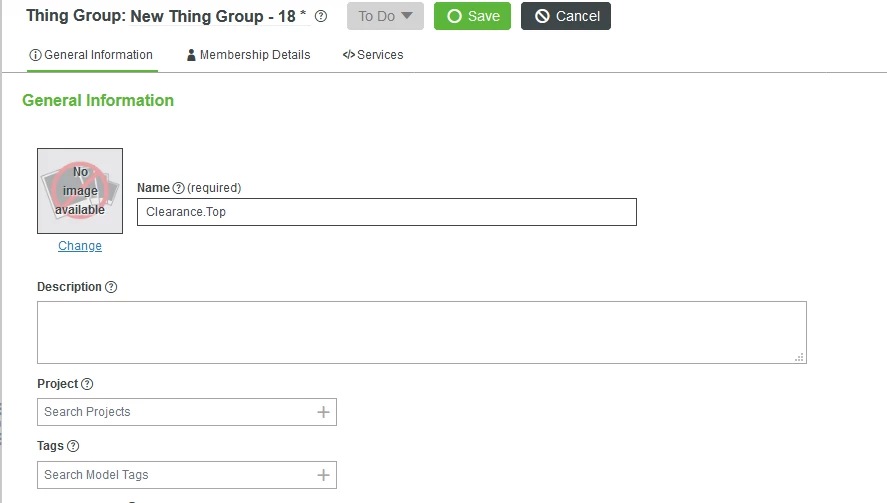
4. Set the Project field to an existing Project (ie, PTCDefaultProject) and click Save.
5. Click the Services tab and click the play button to execute the AddMembers Service.
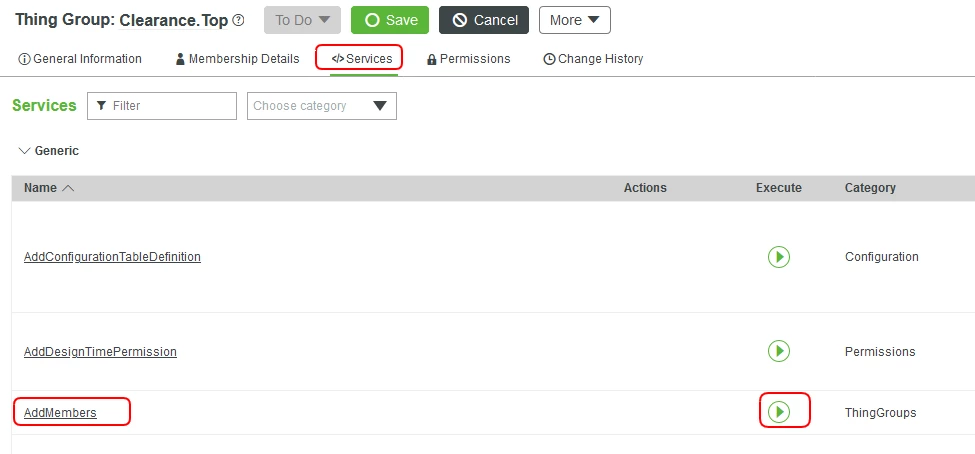
6. Click on the members Input Info Table and click the + Add button.
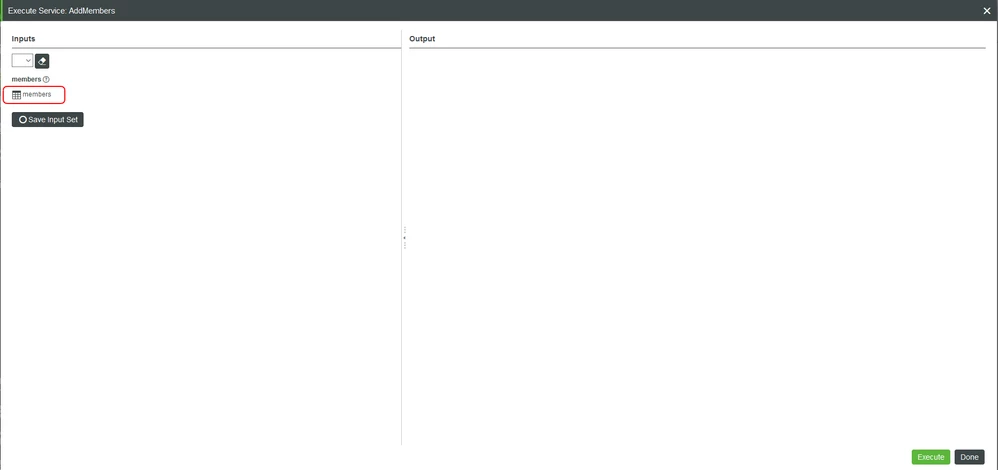
7. Enter TopSecretDocuments as the name of the member and Thing as the type.
8. Click Add and Save. Set the Project field to an existing Project (ie, PTCDefaultProject).
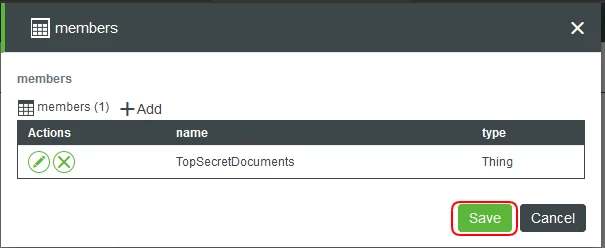
9. With you members set, click Execute.
10. Repeat steps 1-9 to create two more Thing Groups and add the other File Repository Entities that we created earlier. Name these Thing Groups Clearance.Public and Clearance.HumanResources. If we wanted to, we could create a Thing Group to add here as a member of another Thing Groups’ hierarchy.
Thing Group Permissions
Time to set the permissions. With the Clearance.Top Thing Group selected, follow the below instructions. As mentioned before, in a production system, you would have more Users and User Groups to completely setup this scenario.
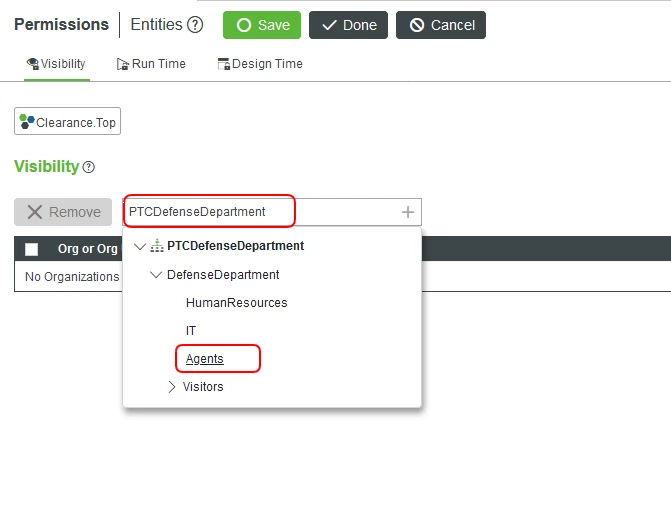
1. Click Permissions.
2. For Visibility, enter PTCDefenseDepartment into the filter.
3. Expand the Organization and select the Agents unit and click Save.
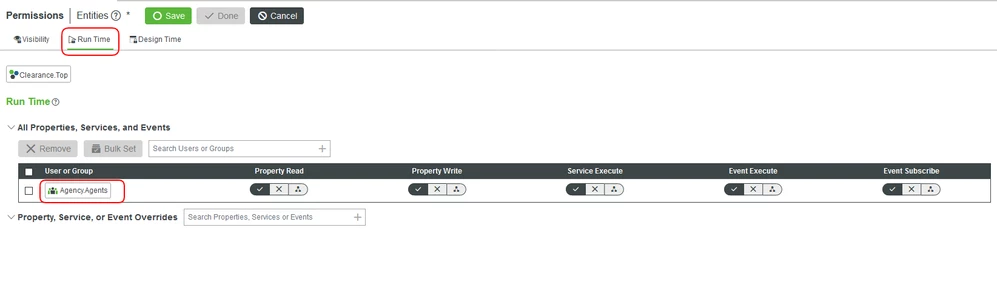
5. Set the permissions for the Agency.Agents User Group to have full access as shown below:
7. Repeat steps 1-6 for our other security clearance Thing Groups. Set the permissions to a department and User Group that you see fit.
Step 7: Next Steps
Congratulations! You've successfully completed the Securing Resources and Private Data guide.
In this guide, you learned how to:
- Securing data and private information
- Use Services, Alerts, and Subscriptions to handle processes without human interaction
- Handling group and organization permissions
The next guide in the Utilizing ThingWorx to Secure Your Aerospace and Defense Systems learning path is Connecting External Databases and Model.
Learn More
We recommend the following resources to continue your learning experience:
| Capability | Guide |
| Build | ThingWorx Solutions in Food Industry |
| Build | Design Your Data Model |
| Build | Implement Services, Events, and Subscriptions |
Additional Resources
If you have questions, issues, or need additional information, refer to:
| Resource | Link |
| Community | Developer Community Forum |

