Create An Application Key Guide
- July 27, 2022
- 1 reply
- 8369 views
- Create An Application Key Guide
- Overview
- Step 1: Learning Path Overview
- Step 2: Create Application Key
- Step 3: Next Steps
Create An Application Key Guide
Overview
In order for a device to send data to the Platform, it needs to be authenticated. One authentication method is to use an Application Key. Application Keys, or appKeys, are security tokens used for authentication in ThingWorx. They are associated with a given User and have all of the permissions granted to the User with which they are associated. This is one of the most common ways of assigning permission control to a connected device. NOTE: This guide's content aligns with ThingWorx 9.3. The estimated time to complete this guide is 30 minutes.
Step 1: Learning Path Overview
This guide explains the steps to create a ThingWorx Application Key, and is part of a Learning Path.
You can use this guide independently from the full Learning Path. If you want to learn to create a ThingWorx Application Key, this guide will be useful to you. When used as part of the Industrial Plant Learning Path, you should already have installed ThingWorx Kepware Server. We will use the Application Key to send information from ThingWorx Kepware Server into ThingWorx Foundation.
Other guides demonstrate Foundation's Mashup Builder to construct a website dashboard that displays information from ThingWorx Kepware Server. We hope you enjoy this Learning Path.
Step 2: Create Application Key
Application Keys are assigned to a specific User for secure access to the platform.
Using the Application Key for the default User (Administrator) is not recommended. If administrative access is absolutely necessary, create a User and place the User as a member of the SecurityAdministrators and Administrators User groups.
Create the User the Application Key will be assigned to.
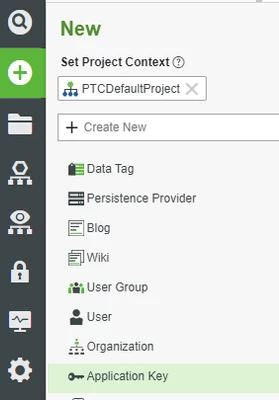
1. On the Home screen of Composer click + New.
2. In the dropdown list, click Applications Key.
3. Give your application key a name (i.e. MyAppKey).
4. If Project is not already set, click the + in the Project text box and select the PTCDefaultProject.
5. Set the User Name Reference to a User you created.
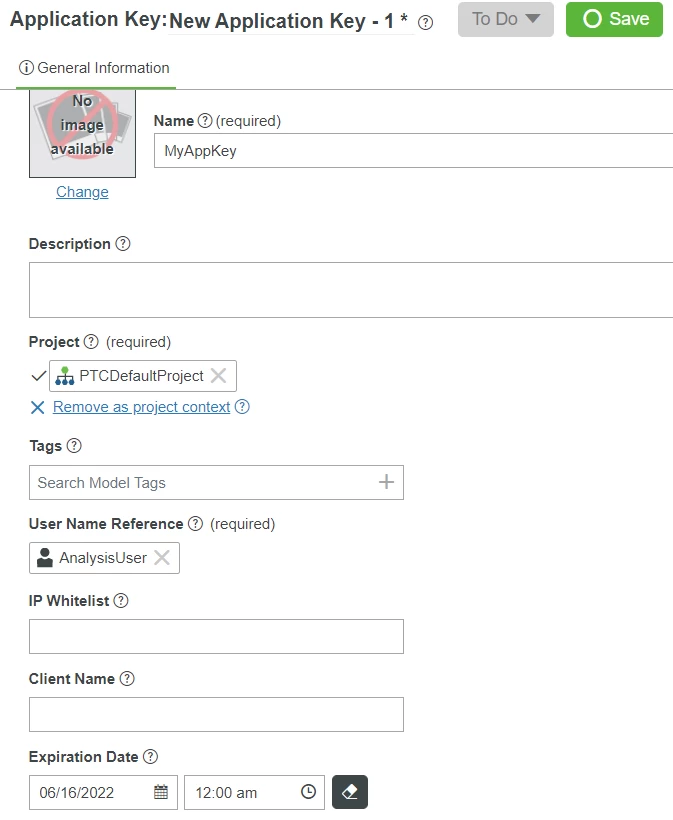
6. Update the Expiration Date field, otherwise it will default to 1 day.
7. Click Save.
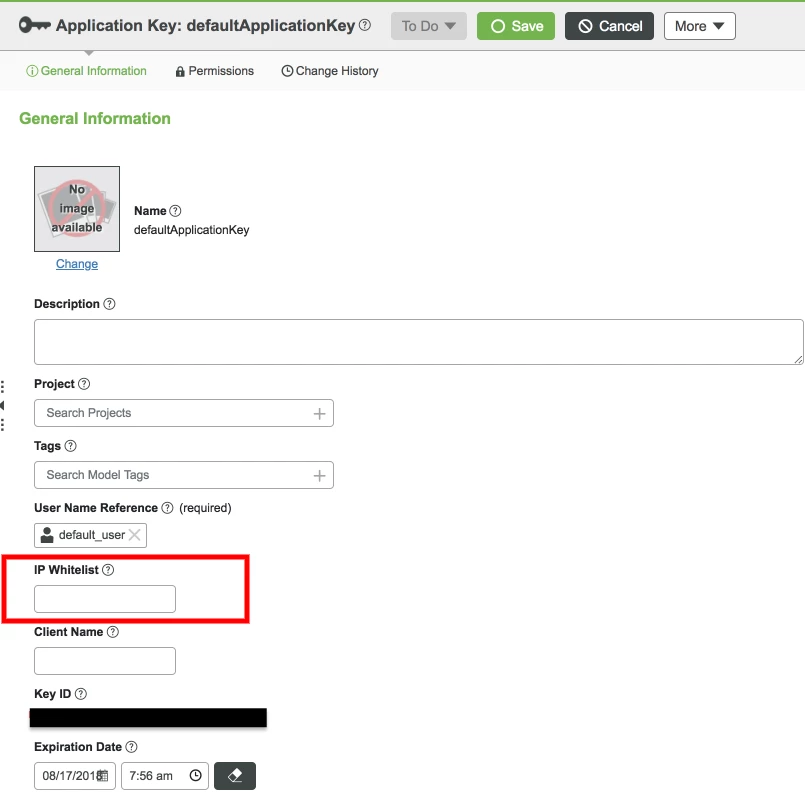
A Key ID has been generated and can be used to make secure connections.
IP Whitelisting for Application Keys
One of the features of an Application Key is the ability to set an IP whitelist. This allows the server to specify that only certain IP addresses should be able to use a given Key ID for access. This is a great way to lock down security on the platform for anything that will maintain a static IP address.
For example, connected Web-based business systems may have a static IP from which all calls should be made. Similarly, you can use wildcards to specify a network to narrow the range of IP addresses allowed while still offering some flexibility for devices with dynamic IP addresses.
Extremely mobile devices should likely not attempt to implement this, however, as they will often change networks and IP addresses and may lose the ability to connect when the IP whitelist feature is used.
Interact with Application Keys Programmatically
Service Name | Description |
GetKeyID | Returns the ID of this Application Key |
GetUserName | Get the username associated with this Application Key |
IsExpired | Returns if this Application Key is expired |
ResetExpirationDateToDefault | Resets the expiration date of the Application Key to the default time based on configuration in the UserManagement subsystem |
SetClientName | Sets the client name for this Application Key |
SetExpirationDate | Sets the expiration date of this Application Key to a provided date |
SetIPWhiteList | Sets the values for the IP whitelist for this Application Key |
SetUserName | Sets the associated user name for this Application Key |
Tip: To learn more about Application Keys, refer to the Help Center
Step 3: Next Steps
Congratulations! You have successfully created an application key. We hope you found this guide useful.
The next guide in the Connect and Monitor Industrial Plant Equipment learning path is Install ThingWorx Kepware Server.
The next guide in the Azure MXChip Development Kit learning path is Connect Azure IoT Devices.
The next guide in the Medical Device Service learning path is Use the Edge MicroServer (EMS) to Connect to ThingWorx.
The next guide in the Using an Allen-Bradley PLC with ThingWorx learning path is Model an Allen-Bradley PLC.

