- Community
- ThingWorx
- ThingWorx Developers
- Connection to Git repository using on-prem GitLab ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Connection to Git repository using on-prem GitLab fails due to SSL error
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify Moderator
Connection to Git repository using on-prem GitLab fails due to SSL error
We are trying to use the Git Backup extension 2.0.2 on ThingWorx 8.4.1 with GitLab community edition hosted on-premises. When trying to push to the repository this fails with an error message (server FQDN has been modified):
Push Error: org.eclipse.jgit.api.errors.TransportException: https://enterhostname.customer.local/iot/thingworx-test.git: Secure connection to https://enterhostname.customer.local/iot/thingworx-test.git could not be stablished because of SSL problems at org.eclipse.jgit.api.PushCommand.call(PushCommand.java:180) at gb.GitBackupTemplate.Push(GitBackupTemplate.java:156) at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method) at sun.reflect.NativeMethodAccessorImpl.invoke(Unknown Source) at sun.reflect.DelegatingMethodAccessorImpl.invoke(Unknown Source) at java.lang.reflect.Method.invoke(Unknown Source) at com.thingworx.common.processors.ReflectionProcessor.processService(ReflectionProcessor.java:261) at com.thingworx.handlers.ReflectionServiceHandler.processService(ReflectionServiceHandler.java:50) at com.thingworx.handlers.ServiceHandlerBase.processServiceWithMetrics(ServiceHandlerBase.java:48) at com.thingworx.things.Thing.processServiceRequestDirect(Thing.java:8306) at com.thingworx.things.Thing.processAPIServiceRequest(Thing.java:8244) at com.thingworx.webservices.BaseService.handleInvoke(BaseService.java:3228) at com.thingworx.webservices.BaseService.service(BaseService.java:499) at javax.servlet.http.HttpServlet.service(HttpServlet.java:741) at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:231) at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166) at org.apache.tomcat.websocket.server.WsFilter.doFilter(WsFilter.java:53) at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:193) at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166) at com.thingworx.security.contenttype.ContentTypeFilter.doFilter(ContentTypeFilter.java:138) at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:193) at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166) at com.thingworx.security.filter.ValidationFilter.doFilter(ValidationFilter.java:22) at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:193) at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166) at com.thingworx.security.authentication.AuthenticationFilter.propagateRequest(AuthenticationFilter.java:541) at com.thingworx.security.authentication.AuthenticationFilter.doFilter(AuthenticationFilter.java:210) at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:193) at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166) at org.tuckey.web.filters.urlrewrite.RuleChain.handleRewrite(RuleChain.java:176) at org.tuckey.web.filters.urlrewrite.RuleChain.doRules(RuleChain.java:145) at org.tuckey.web.filters.urlrewrite.UrlRewriter.processRequest(UrlRewriter.java:92) at org.tuckey.web.filters.urlrewrite.UrlRewriteFilter.doFilter(UrlRewriteFilter.java:389) at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:193) at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166) at com.thingworx.security.filter.ClickjackFilter.doFilter(ClickjackFilter.java:207) at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:193) at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166) at com.thingworx.security.filter.ProhibitIfNotLeaderFilter.doFilter(ProhibitIfNotLeaderFilter.java:120) at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:193) at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166) at com.thingworx.security.filter.HttpResponseHeadersFilter.doFilter(HttpResponseHeadersFilter.java:173) at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:193) at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:166) at org.apache.catalina.core.StandardWrapperValve.invoke(StandardWrapperValve.java:202) at org.apache.catalina.core.StandardContextValve.invoke(StandardContextValve.java:96) at org.apache.catalina.authenticator.AuthenticatorBase.invoke(AuthenticatorBase.java:526) at org.apache.catalina.core.StandardHostValve.invoke(StandardHostValve.java:139) at org.apache.catalina.valves.ErrorReportValve.invoke(ErrorReportValve.java:92) at org.apache.catalina.valves.AbstractAccessLogValve.invoke(AbstractAccessLogValve.java:678) at org.apache.catalina.core.StandardEngineValve.invoke(StandardEngineValve.java:74) at org.apache.catalina.connector.CoyoteAdapter.service(CoyoteAdapter.java:343) at org.apache.coyote.http11.Http11Processor.service(Http11Processor.java:408) at org.apache.coyote.AbstractProcessorLight.process(AbstractProcessorLight.java:66) at org.apache.coyote.AbstractProtocol$ConnectionHandler.process(AbstractProtocol.java:860) at org.apache.tomcat.util.net.Nio2Endpoint$SocketProcessor.doRun(Nio2Endpoint.java:1676) at org.apache.tomcat.util.net.SocketProcessorBase.run(SocketProcessorBase.java:49) at org.apache.tomcat.util.net.AbstractEndpoint.processSocket(AbstractEndpoint.java:1087) at org.apache.tomcat.util.net.Nio2Endpoint$Nio2SocketWrapper$2.completed(Nio2Endpoint.java:589) at org.apache.tomcat.util.net.Nio2Endpoint$Nio2SocketWrapper$2.completed(Nio2Endpoint.java:567) at org.apache.tomcat.util.net.SecureNio2Channel$1.completed(SecureNio2Channel.java:968) at org.apache.tomcat.util.net.SecureNio2Channel$1.completed(SecureNio2Channel.java:897) at sun.nio.ch.Invoker.invokeUnchecked(Unknown Source) at sun.nio.ch.Invoker$2.run(Unknown Source) at sun.nio.ch.AsynchronousChannelGroupImpl$1.run(Unknown Source) at java.util.concurrent.ThreadPoolExecutor.runWorker(Unknown Source) at java.util.concurrent.ThreadPoolExecutor$Worker.run(Unknown Source) at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61) at java.lang.Thread.run(Unknown Source) Caused by: org.eclipse.jgit.errors.TransportException: https://enterhostname.customer.local/iot/thingworx-test.git: Secure connection to https://enterhostname.customer.local/iot/thingworx-test.git could not be stablished because of SSL problems at org.eclipse.jgit.transport.TransportHttp.handleSslFailure(TransportHttp.java:619) at org.eclipse.jgit.transport.TransportHttp.connect(TransportHttp.java:569) at org.eclipse.jgit.transport.TransportHttp.openPush(TransportHttp.java:435) at org.eclipse.jgit.transport.PushProcess.execute(PushProcess.java:160) at org.eclipse.jgit.transport.Transport.push(Transport.java:1310) at org.eclipse.jgit.api.PushCommand.call(PushCommand.java:169) ... 68 more Caused by: javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target at sun.security.ssl.Alerts.getSSLException(Unknown Source) at sun.security.ssl.SSLSocketImpl.fatal(Unknown Source) at sun.security.ssl.Handshaker.fatalSE(Unknown Source) at sun.security.ssl.Handshaker.fatalSE(Unknown Source) at sun.security.ssl.ClientHandshaker.serverCertificate(Unknown Source) at sun.security.ssl.ClientHandshaker.processMessage(Unknown Source) at sun.security.ssl.Handshaker.processLoop(Unknown Source) at sun.security.ssl.Handshaker.process_record(Unknown Source) at sun.security.ssl.SSLSocketImpl.readRecord(Unknown Source) at sun.security.ssl.SSLSocketImpl.performInitialHandshake(Unknown Source) at sun.security.ssl.SSLSocketImpl.startHandshake(Unknown Source) at sun.security.ssl.SSLSocketImpl.startHandshake(Unknown Source) at sun.net.www.protocol.https.HttpsClient.afterConnect(Unknown Source) at sun.net.www.protocol.https.AbstractDelegateHttpsURLConnection.connect(Unknown Source) at sun.net.www.protocol.http.HttpURLConnection.getInputStream0(Unknown Source) at sun.net.www.protocol.http.HttpURLConnection.getInputStream(Unknown Source) at java.net.HttpURLConnection.getResponseCode(Unknown Source) at sun.net.www.protocol.https.HttpsURLConnectionImpl.getResponseCode(Unknown Source) at org.eclipse.jgit.transport.http.JDKHttpConnection.getResponseCode(JDKHttpConnection.java:99) at org.eclipse.jgit.util.HttpSupport.response(HttpSupport.java:202) at org.eclipse.jgit.transport.TransportHttp.connect(TransportHttp.java:500) ... 72 more Caused by: sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target at sun.security.validator.PKIXValidator.doBuild(Unknown Source) at sun.security.validator.PKIXValidator.engineValidate(Unknown Source) at sun.security.validator.Validator.validate(Unknown Source) at sun.security.ssl.X509TrustManagerImpl.validate(Unknown Source) at sun.security.ssl.X509TrustManagerImpl.checkTrusted(Unknown Source) at sun.security.ssl.X509TrustManagerImpl.checkServerTrusted(Unknown Source) ... 89 more Caused by: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target at sun.security.provider.certpath.SunCertPathBuilder.build(Unknown Source) at sun.security.provider.certpath.SunCertPathBuilder.engineBuild(Unknown Source) at java.security.cert.CertPathBuilder.build(Unknown Source) ... 95 more
The SSL-certificate of the GitLab-webserver is trusted by Google Chrome when I try to access GitLab from the ThingWorx server.
There seems to be something else that has to be configured to make this working. We are using a self-signed certificate in .local domain.
Any help is appreciated. Thank you.
- Labels:
-
Extensions
-
Troubleshooting
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify Moderator
Hello,
I would think that your self-signed certificate is an issue. The fact that you "trust" it in your Chrome doesn't mean that the JVM running ThingWorx would know anything about it and/or do the same. A couple of suggestions:
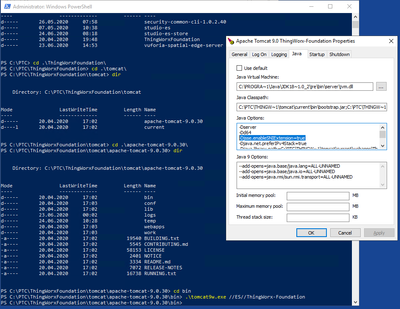
1. Add this self-signed certificate to ThingWorx' JVM trust store. You'll find plenty of examples of how to do it, e.g. here.
2. Don't use self-signed certificates, get a proper domain name and certify it, at least via LetsEncrypt.
Regards,
Constantine
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify Moderator
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify Moderator
Hi @pjahn
I am having same situation like you and getting same error.
Please share the steps of resolution if you have resolved it. Thank you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Notify Moderator
Your self signed cert has to be added into the truststore/keystore used by Tomcat. Also - if ThingWorx has been installed using the installer - you also might have to consider the setting for service name indication (SNIExtension)
- Tags:
- HA