Azure AD and Thingworx SSO configuration
Hi all,
I'm trying to configure SSO for Thingworx, I followed this link, I got stuck at 'Browser SSO' configuration. (PFB PNG for reference)
Could any one help me with this.
Thanks in advance
/VR
Hi all,
I'm trying to configure SSO for Thingworx, I followed this link, I got stuck at 'Browser SSO' configuration. (PFB PNG for reference)
Could any one help me with this.
Thanks in advance
/VR
Hi,
Steps to create a self-signed Application Layer certificate for PingFederate
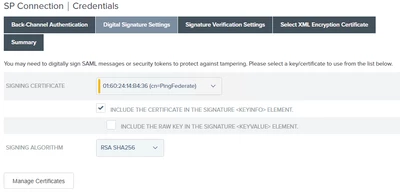
When you visit this tab for the first time, there will be no certificate in the dropdown list. You can import the public part of the Thingworx signing certificate and choose it as Signature Verification Certificate
Enter your E-mail address. We'll send you an e-mail with instructions to reset your password.